Fastman Access Manager
Control what users can do, not just what they can see.
Manage user access to functions and actions with precision and ease.
Control which functions users can access and perform
Support compliance with licensing and regulatory requirements
Reduce information security risks with precise access management
When audits show your users are doing things they shouldn’t be able to, what do you do?
Extended ECM provides no way to limit access to individual functions leaving your organisation at high risk of information security and compliance failures

Do you...
- Rely on end-user training in order to comply with policies
- Create internal quick-fixes and reports to resolve errors once they’ve occurred
- Pay fines or purchase full-user licenses for policy over-runs
- Trust that users will only do what they are supposed to
You should be able to control the functions your users can perform.
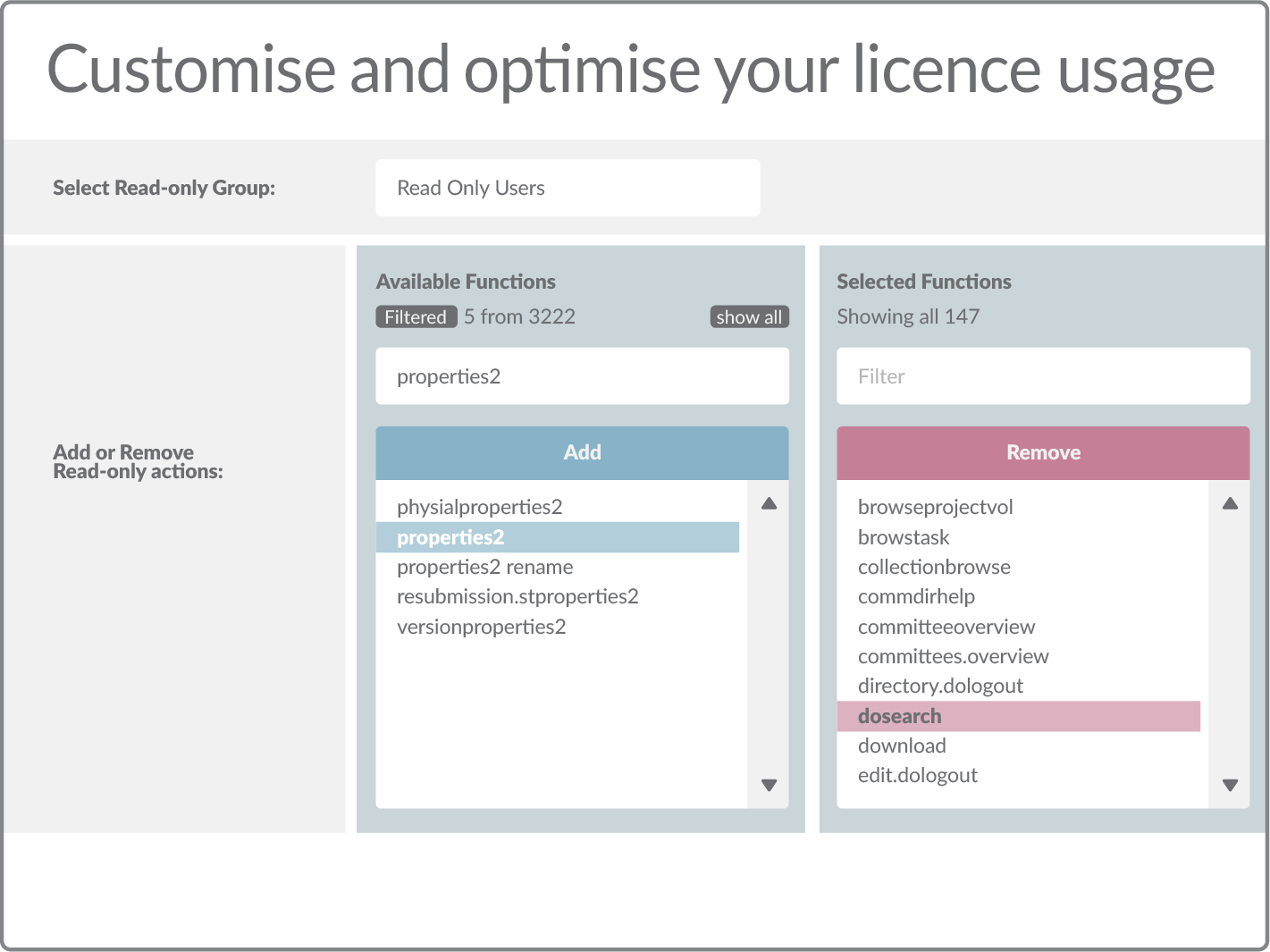
Manage exactly what functions your users can perform
It’s your data, it’s your choice. By using a simple administration interface, Fastman Access Manager allows your system admins to manage exactly what functions your users can and can not perform. This list can be readily tailored and customised to enforce strict belt and braces compliance, or can be lifted for individuals
Ensure compliance
Access Manager provides complete control over the functions that users have access to, ensuring compliance with regulatory and license obligations, and minimising information security risks.
No more penalties and fines
Fastman Access Manager stops users from acting out of their licence bounds, preventing expensive penalties and fines. With Fastman Access Manager, you’ll never have to worry about audits anymore
Off-the-shelf, operational within an hour
As an easy to configure Content Suite module, Fastman Access Manager requires minimal professional services or supplementary development effort. It is fast to deploy, more robust and more cost-effective than any alternative option.

Ensure your information security and license compliance risks are under control
Many organizations struggle to manage the functions their users can perform within their OpenText/SAP© Extended ECM platform. Access Manager provides complete control over the functions that users have access to, ensuring compliance with license requirements and minimizing information security risks.
At Fastman we understand your challenges
We understand the challenges you have with access control, which is why numerous global organisations have implemented Access Manager as a proven, out-of-the-box solution
Some of our customers










Related Assets
It's time to trust your information…
1. Book a call
We will demonstrate how easy it is to control the functions your users can perform.

2. Evaluate for free
Get a no-cost evaluation that you can test within your own environment.
.png)
3. Deploy and enjoy
Achieve your information management objectives quickly and effectively.